Participating at HackYeah
After we all had a blast at Junction 2024, my uni friends and I decided that we would go for another round of the hackathon experience in 2025. This time it would not be the same one. Variety is the spice of life, after all. Instead, we settled on HackYeah in Kraków. “The biggest stationary hackathon in Europe”, as they claim.
This time around, some more people joined our group, and we ended up going as ten people (compared to last year’s eight). Since the team size limit happened to be five again, this was quite welcome, as it allowed us to form two full teams as opposed to leaving one team smaller.
Again, there were several challenges to choose from, including ones made by partner companies and non-branded ones created by the HackYeah team. Additionally, HackYeah included several stage talk segments where relevant figures from Poland talked about topics about Polish and European tech. This included talks about applications in defence, medicine, and general AI.
Instead of competing in one of the regular hackathon challenges, we ended up joining the hackathon’s own 2084 CTF1. The reason being that both events were limited to only 24 h, which we felt would be too little for developing a project but just fine for some security challenges. This was the first CTF I played outside the Platypwnies (my university’s cybersecurity club and CTF team). I believe we placed in the top 10, but I cannot find the scoreboard any longer to double-check. We had a great time solving challenges either way.
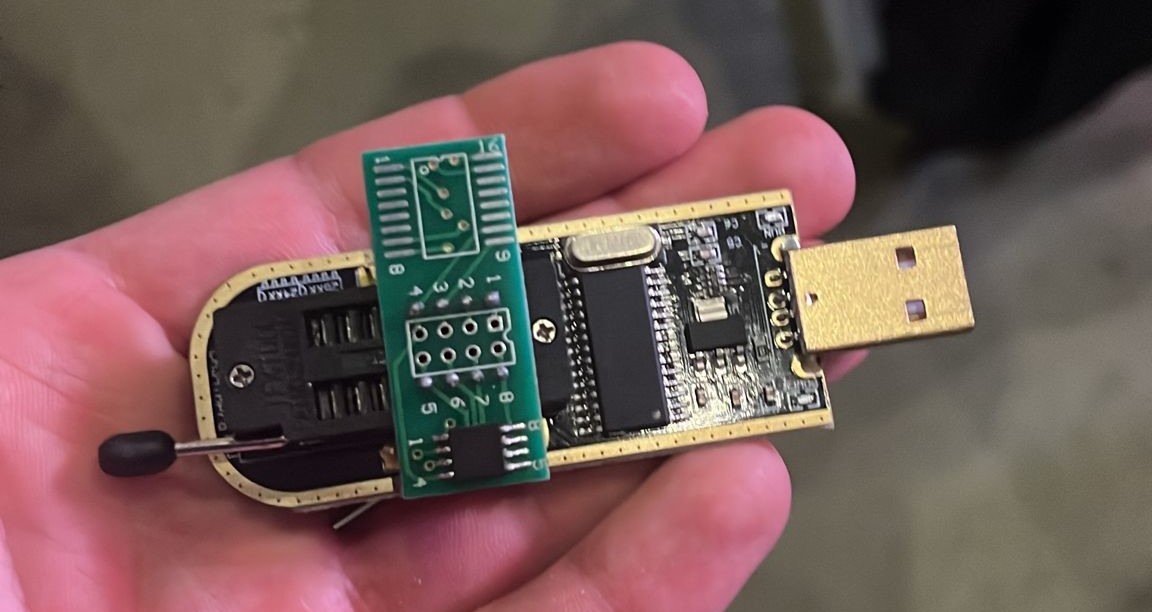 They included discovering website vulnerabilities, finding secret messages in PDF, image, video & audio files, capturing network transmissions, and performing decryptions. And most interestingly, as this was entirely an in-person event, there were hardware challenges where we could pick up some devices prepared by the organisers and, for example, extract information from some (possibly protected) memory on it. One example is on the right.
They included discovering website vulnerabilities, finding secret messages in PDF, image, video & audio files, capturing network transmissions, and performing decryptions. And most interestingly, as this was entirely an in-person event, there were hardware challenges where we could pick up some devices prepared by the organisers and, for example, extract information from some (possibly protected) memory on it. One example is on the right.
